It has been six years since we've began LINE GAME, and over those six years we've been through many experiences. Today, I'd like to share some lessons we've learned along the six-year journey of LINE GAME, specifically focusing on how we used monitoring to prevent game cheating.
When I say "game cheat" in this blog post, I am referring to malicious users (abusers) using exploitative means to give themselves an advantage in the game, such as engaging in the act of modifying apps or manipulating data.
LINE takes the responsibility of keeping the experience of our LINE GAME users playing our games as safe as possible, using various methods to monitor, analyze, and respond to abusers after we release a game.
Mobile gaming has seen huge growth in recent years, and the games that we develop or publish are also mostly mobile games available on iOS or Android. So the focus of this post will also be on mobile gaming apps, more specifically on monitoring and responding to user activity after the release of the game more than how to prepare the app beforehand.
About LINE GAME
Before we go in to more detail about game cheats, I'd like to briefly introduce some of the features and characteristics of LINE GAME.
The first feature I'd like to highlight is LINE Login integration. Users can log in to games using their LINE account, which expands their gaming experience in various ways such as allowing them to compete in the leaderboards against their friends, or send useful items that are required to play. LINE Login also allows users to keep their game progress stored on their LINE account so that they can continue where they left off even when they switch phones or carriers.
The second is the two types of currency used in our games. There is "primary currency" that must be purchased using real money, and then there is "secondary currency" that can be purchased with the primary currency. To bring up one of our recent releases as an example, in LINE CHEF (Japanese only), "diamonds" were a primary currency and "coins" were a secondary currency. Primary and secondary currencies can be used to purchase in-game items including loot boxes that contain random items.
The third and last point is that users cannot trade in-game currency or items with other players. Any in-game currency or items obtained by a player can only be used by themselves.
Types of commonly used cheats
Game cheats are hardly something new. Cheats have existed on PC and console games for decades, and they continue to exist today even in the age of online and mobile games that require the use of your mobile phone, or being connected to the internet.
Over the past six years that we've been monitoring abusers in our games, we've identified the following three types to be the most common.
Memory editing
Memory editing is a method of cheating that involves modifying the memory values where a game stores information. For example, someone could search for the value tied to the number of coins or items and change that value. While we will refrain from mentioning any certain memory editing tool or how to use them, memory editing tools are widespread and can be easily found on the internet along with instructions on how to use them, allowing nearly anyone to attempt this form of cheating. The figure below depicts an example of memory editing to change the number of Coins that the player has.
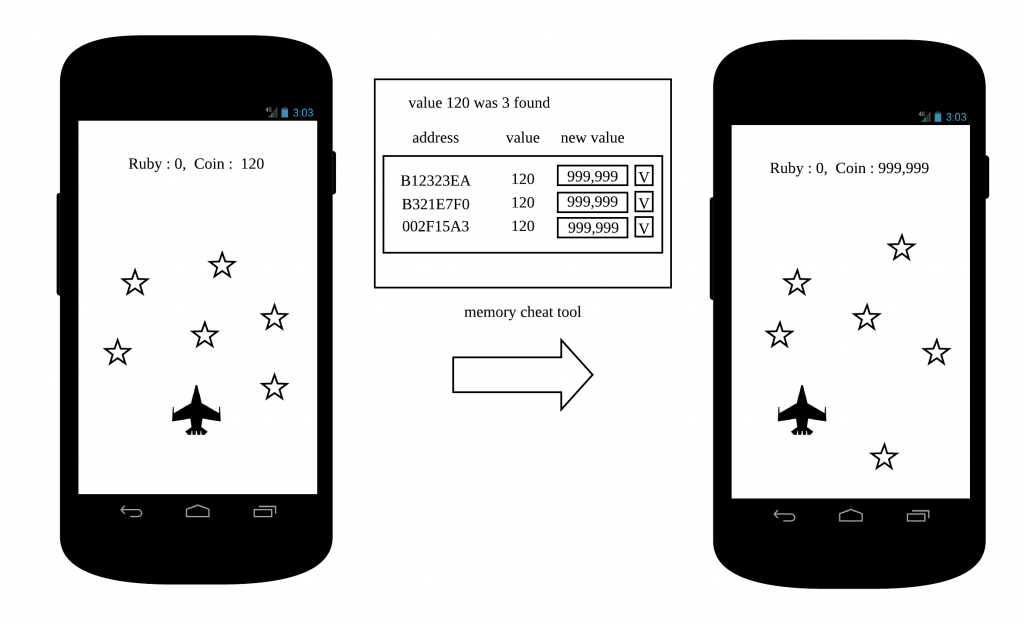
One method of countering memory editing is to encrypt crucial variables used for in-game currency and items.
Packet editing
Packet editing involves the act of editing packets to modify network traffic. Abusers find and analyze packets that are sent from the game, to send false information to the server, pretending that they have a certain number of coins or items.
Many native games [1] are written so that gameplay takes place on the client-side, and the results are sent to the server afterwards. Even though it requires a certain amount of expertise to intercept and edit packets that are sent on these types of games, packet editing attempts occur regularly. The figure below depicts an example of packet editing, sending false information to the server.

You can counter packet editing by having the server perform a check whenever it receives gameplay results (parameters) from a client. You could also limit the number of items that can be gained at a time to minimize the impact that could be caused by cheats.
Binary file editing
Binary file editing is the act of editing the binary files of the game client itself. For example, abusers would edit the .apk file for Android games and the .ipa file for iOS games. Binary files contain numerous variables and logic that determines how the game calculates actions. Abusers can gain currency or items, make allies stronger, or make enemies weaker by modifying these variables and logic.
As binary files are converted to executable files that can be run on the corresponding operating system used on each mobile phone, they cannot be easily modified. Because of this, binary editing cheats are mostly done by individuals who have expertise in game development, and have the ability to reverse engineer the game [2]. The figure below depicts an example of binary editing, where the EXP value has been edited.

Preventing binary file editing is difficult, as anyone can easily extract a game client module that is installed on their mobile phone and tamper with it.
Obfuscation can somewhat hinder the attempts to reverse engineer a binary file, but it is not a perfect solution. To an individual who has the means and the expertise, it is only a matter of time before they eventually crack open a client module. Even so, obfuscating your code is still recommended as it will will definitely prevent your game from being easily manipulated. Just keep in mind that there are many things to consider when going the route of obfuscation. The file size of your game may become larger, or it could increase the boot time of your game as well. We won't go into too much detail about obfuscation here.
As you may have noticed from the three cheating methods discussed above, they mostly involve tampering with the client. Protecting your client from attacks requires you to be vigilant of new and popular cheating methods, and to improve your client module. You may sometimes find yourself performing similar improvements over and over again, but don't consider that time wasted. It will definitely pay off in the end.
Monitoring to prevent cheating
As I've briefly mentioned, we at LINE take game hacking attempts seriously, and are always putting in more effort to make sure that we can prevent them. As much as protecting your client from hacking is important, we also consider setting up a monitoring system to be just as important for preventing damage caused by cheating.
Native games running in a mobile environment often include various features in the client module that allow the client to accurately interpret when the user swings a sword, or evades an attack. As mentioned above, client modules can eventually be cracked and that is why they are the number one target for abusers. That is why began to include indicators related to client manipulation in our monitoring process, so that we would be able to respond [3] to such attempts when we detect them.
Our monitoring process operates on three core pillars: one is to check whether there was an attempt to "exploit the game client," another is to check whether there was an attempt to "exploit the game server with invalid data" (this requires a dedicated module included with our game clients, but that is not a topic that we will be discussing in this post), the last is to check whether there were attempts to "abuse the refund system or use other methods to cheat."
Monitoring malicious behavior on the game client
We use the following indicators when monitoring malicious behavior on the game client.
- How many users have installed and launched the game on a non-standard environment (This includes devices that have been rooted, jailbroken, or apps running on an emulator)
- How many users have installed and launched a cheating tool
- How many users have installed and launched a modified version of the game that has a different hash value compared to the normal binary file
- Are there records of logging in with different accounts on a single device
A user that has either rooted or jailbroken their device and installed a cheating tool would have likely tried to use the memory editing method. If this indicator suddenly increases during our monitoring process we can assume that there is an abuser trying to exploit the memory editing method.
Someone that is repeatedly uninstalling and installing the game on an emulator is likely rerolling [4]. If this indicator suddenly increases during our monitoring process, we can assume that someone has bought an account from another user (although it is not always the case).
If there are login attempts from multiple accounts on a single device, we can assume that a proxy is attempting to cheat instead of the original owner of the device.
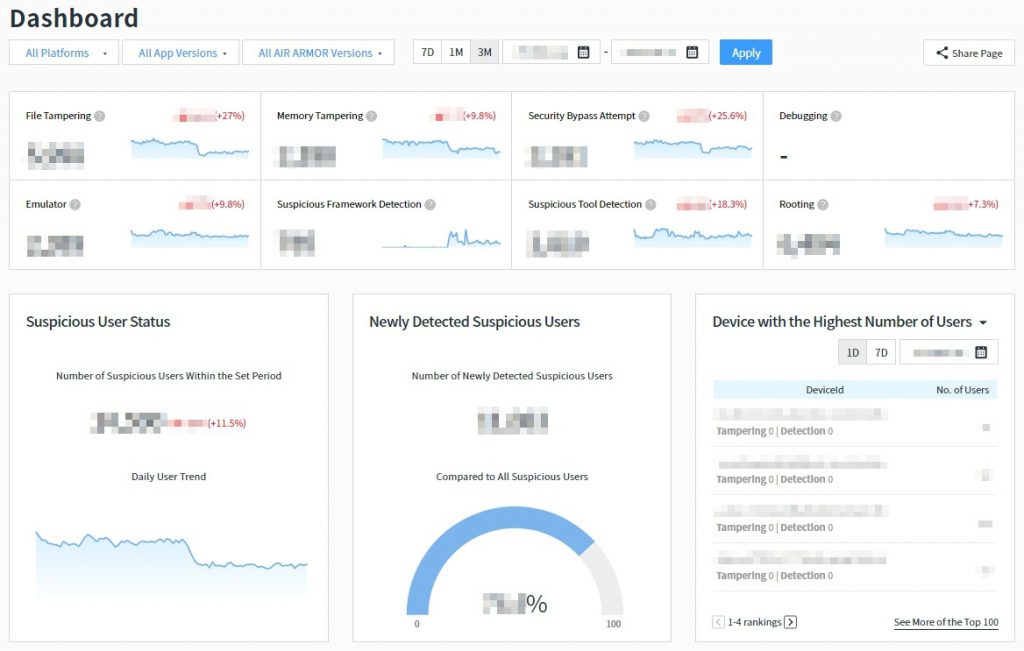
The figure below is an excerpt of our monitoring data where we have detected attempts of running our games on a rooted or jailbroken device, or on an emulator, or running any cheating tools. By monitoring these indicators, we are able to detect any potential abusers.

If we detect users that have installed a binary file that has a different hash value compared to a genuine one, we can assume that these users are trying to cheat by editing binary files.
The figure below is an excerpt of our monitoring data where we have detected binary files that had abnormal hash values. In situations like this, it is likely that the edited binary file has been distributed online and in use by several users. Currently, our system is set up to detect abnormal binary files, allowing us to monitor who used these edited files at what time.

We monitor the indicators above daily, so that we can assess how widespread a certain exploit is, and to prevent an abuser from using that exploit to influence the game. Below is a screenshot of out monitoring tool's dashboard.
Monitoring invalid data on the game server
We use the following indicators when monitoring malicious behavior on the game server.
- How many users have gained in-game currency that exceeds expected parameters in a single stage
- How many users have recorded scores that exceeds expected parameters in a single stage
- How many users have beaten the game in an abnormally short amount of time
- How many users have more wins than stages played recorded in the logs
For example, if a player earns more in-game currency or score more points than the expected parameters for a single stage, it's likely that they might have made a memory edit or tried to send false packets.
Below is a case where we found a user that had earned a negative amount of in-game currency. The user had used a memory editing cheat to tamper with the variable that store the amount of currency they have, but they mistakenly entered a value that exceeded the range of the exploited variable, resulting in a negative value. If you are using signed integer variables to store in-game currency information, the value can be anywhere between -2,147,483,648 and 2,147,483,647. If a value that exceeds 2,147,483,647 is sent to the variable, an integer overflow will occur, changing the value to a negative number.

A user that ends stages in an unusually short amount of time, or users that have played several stages in quick succession are prime suspects of editing binary files or packets.
If someone were to edit the binary files to change the amount of HP a boss has to 0, they would be able to take down that boss in an abnormally short amount of time. Alternatively, someone could send packets that tell the server that the player has beaten the boss without even fighting it in the first place, beating it several times in an amount of time that would be impossible through normal play.
Below is a case where we found a user that was beating a stage in 5 seconds (considering the amount of time it takes to render the stage on the display, it took less than 5 seconds of actual play time) when it would normally take more than 30 seconds. The user had edited binary files to beat the stage without even playing.

An additional risk is a non-client bot or website that allows users to "play" the game only through packets without even installing the game normally. As these bots and websites only sends packets that are necessary for the game, they leave a small footprint in logs. For example, they may have many win records on the log, without actually having the play records to back them up.
We monitor the indicators above daily, so that we can find out if someone is sending fraudulent data to the server, and to prevent an abuser from using that to influence the game.
Monitoring users who abuse the refund system
Some forms of cheating come from the most unexpected places. One such cheat is to abuse Google's in-app purchase refund policy. Google's in-app purchase policy gives them the right to refund any in-app purchases made on apps that are provided through their digital storefront. Users who intend to abuse the policy work in the steps below.
- The abuser purchases primary currency through an in-app purchase.
- The abuser exchanges the purchased primary currency into in-game items or secondary currency
- The abuser requests a refund through Google
- Google process the refund request via their refund policy
If an abuser follows the steps above to receive a refund without our knowledge of the fact, the abuser would have used the purchased primary currency to buy in-game items and then receive a refund, effectively allowing them to purchase in-game items at no cost.
Using Google's own Voided Purchases API (which provides a list of orders made by the user who has received a refund), you can look out for these attempts. We monitor any refunds made in our games to make sure that they were made legitimately, so that an abuser cannot influence our in-game economy.
In conclusion
Throughout the post, we took a look at some examples of cheats and how we monitor them. If efforts made to prevent the client from being hacked is a "preemptive defense," you could say monitoring abusers and penalizing them for any abuses of the system that they might have caused a form of "retaliation."
Preemptively defending your client from hacks requires you to stay updated with new and advanced cheating methods that appear everyday, and while this is effective, it must be complemented with an effort to monitor and respond to cheating attempts.
If a player were to distribute an edited .ipa file of your game on the internet, the number of users that are using the edited client will skyrocket. The negative effect this will have on your game goes without saying.
Users would be able to easily cheat their way through the game without making any purchases, use cheats that normally wouldn't work unless using a jailbroken device or an emulator, or even use a website that allows them to "play" the game without actually knowing how to install a modified .ipa file on their phone.
However, with a capable monitoring system in place, you can respond to an incident like this before the abusers actually impact your game.
As you can see, an effective monitoring system is a necessity for game security. You can trust us at LINE to make sure that no one cheats in our games and gets away with it!
[1] Games that can run without having to pass through a web browser or another app.
[2] For example, games made using the Unity engine can be analyzed by reverse-engineering the Assembly-CSharp.dll file. If you want to know more about this type of hack, you can read more on the links below.
[3] This refers to the penalties that we would apply to a user if the monitoring results show that they are an abuser. Penalties include confiscation of in-game currency or items obtained through cheating, or account suspensions.
- https://engineering.linecorp.com/ja/blog/unity-from-a-security-engineer-point-of-view/ (Japanese only)
- https://www.slideshare.net/linecorp/cedec2017-line (Japanese only)
[4] Rerolling refers to the act of opening a loot box in the game, uninstalling the game and trying again until the user obtains their desired items..
