Hello again, this is Myoungje Yi (MJ) from LINE's security team. I'd like to share our annual report on running the LINE Security Bug Bounty Program in 2017.
Program scope expansion & donation option
The 'LINE Security Bug Bounty Program' aims to provide LINE users the most secure service by fixing potential vulnerabilities in advance, by getting reports from external security researchers. As we have already mentioned in our previous post, we have expanded the program scope in 2017, which resulted in an increased number of reports submitted. In November 2017, we have added an option allowing reporters to donate their reward.
General information on LINE Bug Security Bug Bounty Program
If this post is making you curious about the program, check out the following pages. We look forward to have you join us.
- Reporting form(requires signing in)
- Terms of use
- Program FAQ
Weekly submission and vulnerability types
In 2017, a sum of 212 reports have been submitted through the program site. The following graph shows the weekly report submissions for the year.
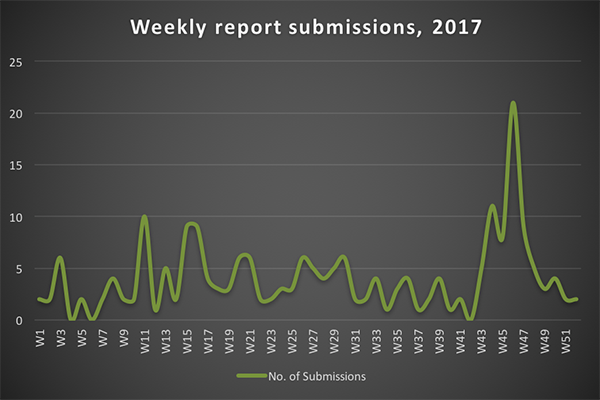
The number of vulnerabilities reported as per duration are as follows:
- Before scope expansion (2017-04-10): 40
- After scope expansion (2017-04-10): 172
- In the first half of 2017: 96
- In the second half of 2017: 116
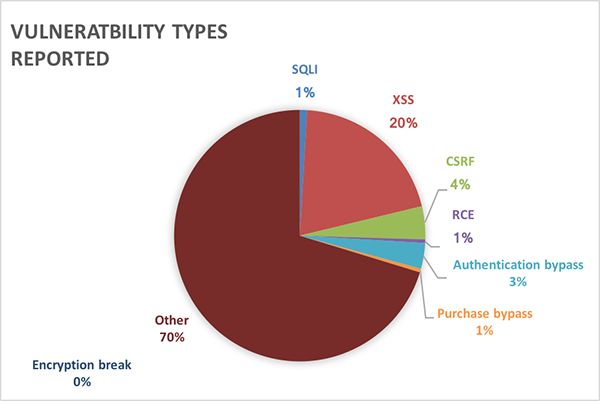
The types of vulnerabilities submitted in 2017 are shown in the following chart.
Visits by country
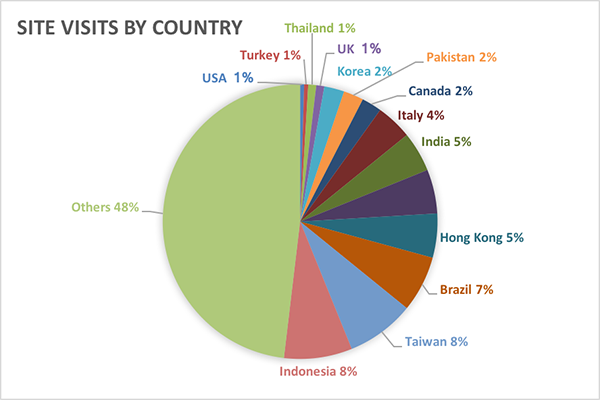
Of the 212 reports received, 11 were from Japan and 201 were from Korea and other countries. The following chart shows you the site visits by country.
Report evaluation
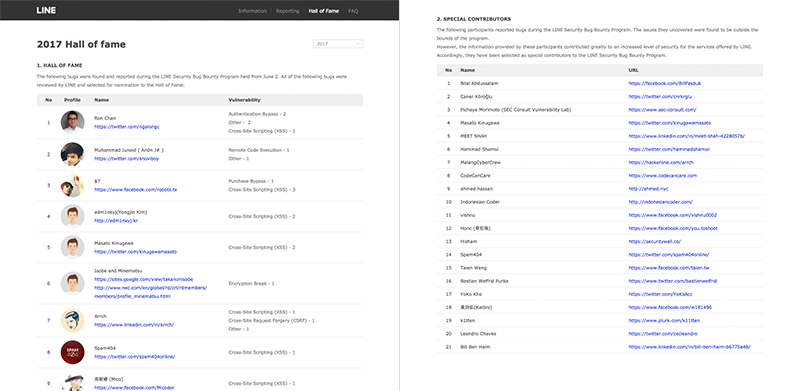
A sum of 45 vulnerabilities have been acknowledged in 2017 including XSS (Cross-site Scripting) and CSRF (Cross-Site Request Forgery). You can see the result on the Hall of fame page. For your information, we put up a notice when the Hall of fame list gets updated.
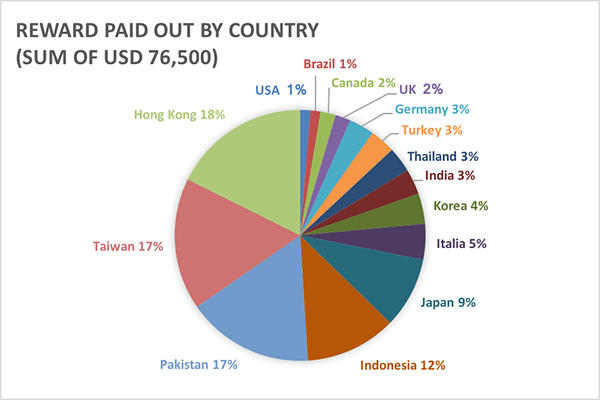
A total of $76,500 (USD) has been paid out as rewards. You can see the proportion of rewards given out by country in the following chart.
The reports evaluated as meaningful to LINE but ineligible for official acknowledgement based on the program's terms have been rewarded as special contributors. In 2017, 21 special contributors have been rewarded, which is quite an increase from 2016, where 8 special contributors had been selected.
Rewards
Reward statistics
| 2015 (Trial) |
2016 (Official launch) |
2017 (Program scope expansion) |
|||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Operation period | Aug 24–Sep 23 | Jun 2–Dec 31 | Jan 1–Dec 31 | ||||||||||||||||||||||||
| Vulnerabilities reported | 194 (Japan: 89, Others: 105) |
97 (Japan: 15, Others: 82) |
212 (Japan: 11, Others: 201) |
||||||||||||||||||||||||
| No. of qualified vulnerabilities | 14 | 13 | 45 | ||||||||||||||||||||||||
| Hall of Fame | 8 | 3 | 11 | ||||||||||||||||||||||||
| Special Contributors | 9 | 8 | 21 | ||||||||||||||||||||||||
| Total reward | USD 44,000 | USD 27,000 | USD 76,500 |
Reward payout process
If a bug reported is acknowledged as a vulnerability, the reporter gets rewarded in the following process:
- A reporter submits a bug report.
- LINE evaluates the bug.
- If the bug is acknowledged as a vulnerability, LINE contacts the reporter regarding the reward.
- The reporter agrees to receive the reward.
- The reporter submits information required for receiving the reward.
- LINE checks the submitted information and documents.
- LINE pays the reward to the reporter.
For detailed information on the reward process, see the Q12 on the FAQ. For your information, the average time taken for the payout after notifying the rewardee was 52 days, in 2017.
Ending notes
Thanks to our reporters, we were able to discover and fix vulnerabilities in advance. The vulnerabilities acknowledged have been fixed, allowing LINE users to enjoy even more secure services.
As mentioned earlier, we have expanded the program scope in accordance with LINE's service expansion and started to allow users to donate their reward. We will continue to expand and develop the LINE Security Bug Bounty Program to continue to reduce the security risks at LINE.
Feel free to report vulnerabilities at the LINE Security Bug Bounty Program site. Your participation is always appreciated. For those of you who are interested, check out our previous posts on the program.
